The EPANET user's dilemma
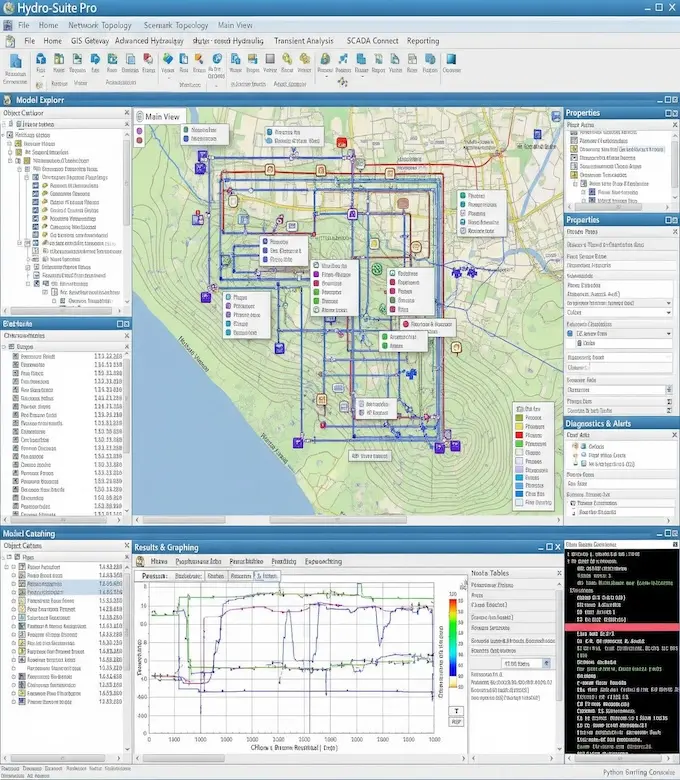
- Classic EPANET is powerful — but clunky and outdated. Workarounds become your workflow — slow and cumbersome.
- Big-name platforms look polished, but they're overpriced and bloated with features you don't need to analyze your network quickly.
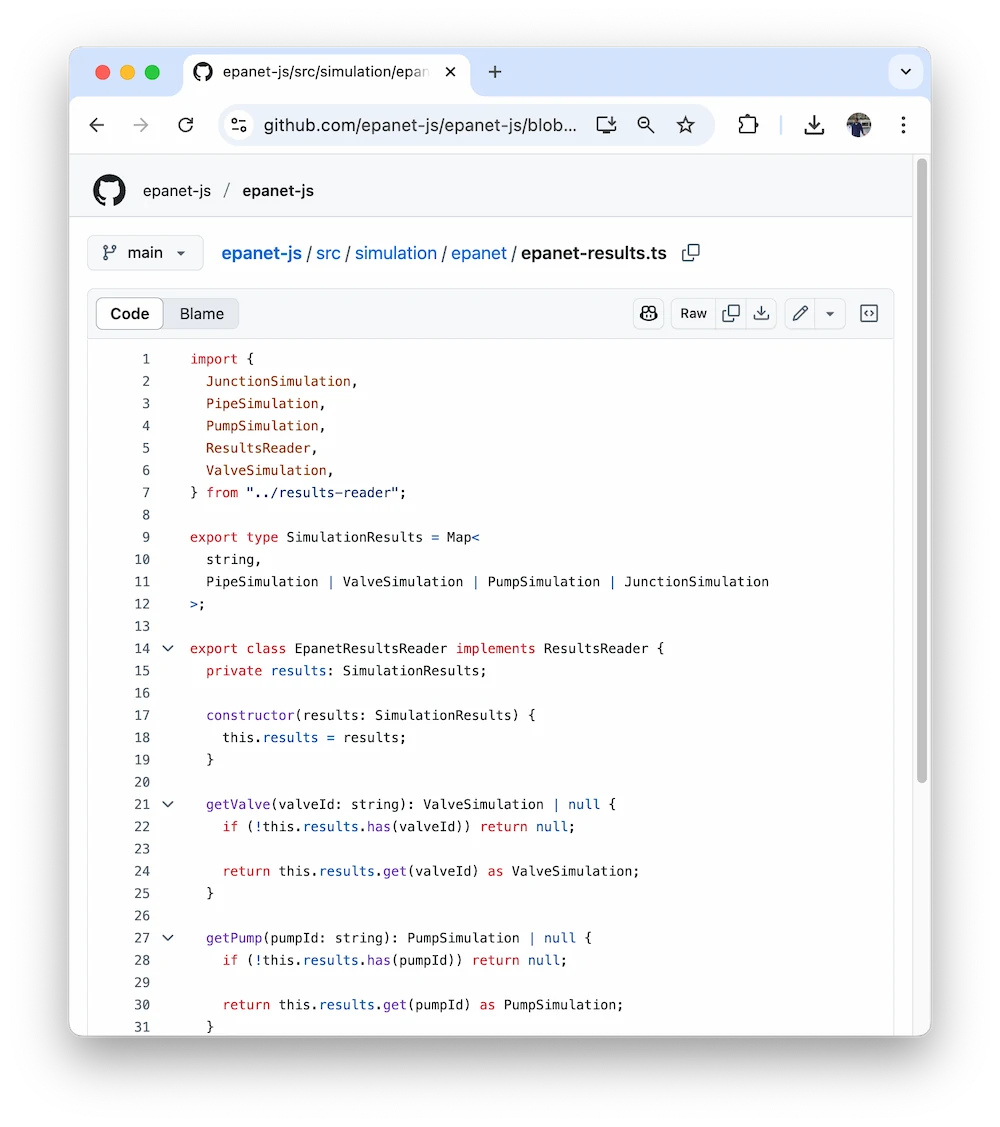
- Modern browser-based tools exist — but they force your data into the cloud, raising privacy and compliance concerns. Plus, they offer little for those doing long-term planning and analysis.
You shouldn't have to choose between speed, security, and affordability just to understand your water networks.